Cofense has stumbled upon a especially tempting phishing trick that makes the use of a wage growth to trap employees to spill their microsoft office 365 credentials.
The spoofed email differs little from other types used in phishing assaults, except this one purportedly comes from a company’s hr branch having a company-wide salary hike to which the intended victim is entitled, wrote milo salvia, of the cofense phishing defense center.
“It is not uncommon, of course, for companies to increase salaries throughout the year. As a result, it wouldn’t be uncommon for an email like this to appear in an employee’s mailbox. Human curiosity compels users to click the embedded link,” he wrote.
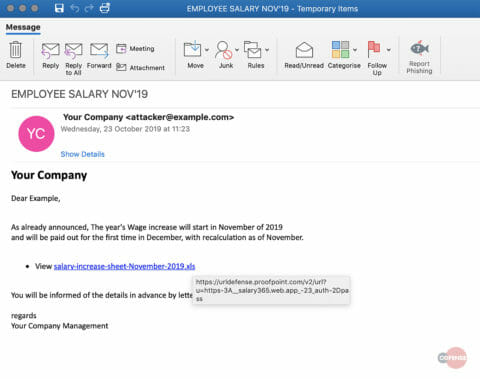
The main tactic being used is convincing the recipients that they’re being connected to a sharepoint report when in reality they’re being redirected to an external url.
As soon as the malicious website is opened, the target is provided with a fake workplace 365 login page. Here the person’s email address is pinned to the username location so only the password needs to be inserted. This mimics many autofill templates. At this factor the attacker has performed his purpose and now has got access to to that organization’s workplace 365 account.


